How to Reduce Onboarding Time with Electronic KYC Solution
In today’s digital world, if your sign-up process takes too long, your potential customers will simply sign out and run straight to your competitors. Here’s where the electronic KYC solution solves the problem exactly.
If the business is struggling with high customer drop-off rates during sign-up, or the compliance team is overwhelmed with multiple paperwork tasks, an electronic KYC solution is the right tool for the business.
Let’s understand modern technology and how it can transform into a seamless onboarding process.
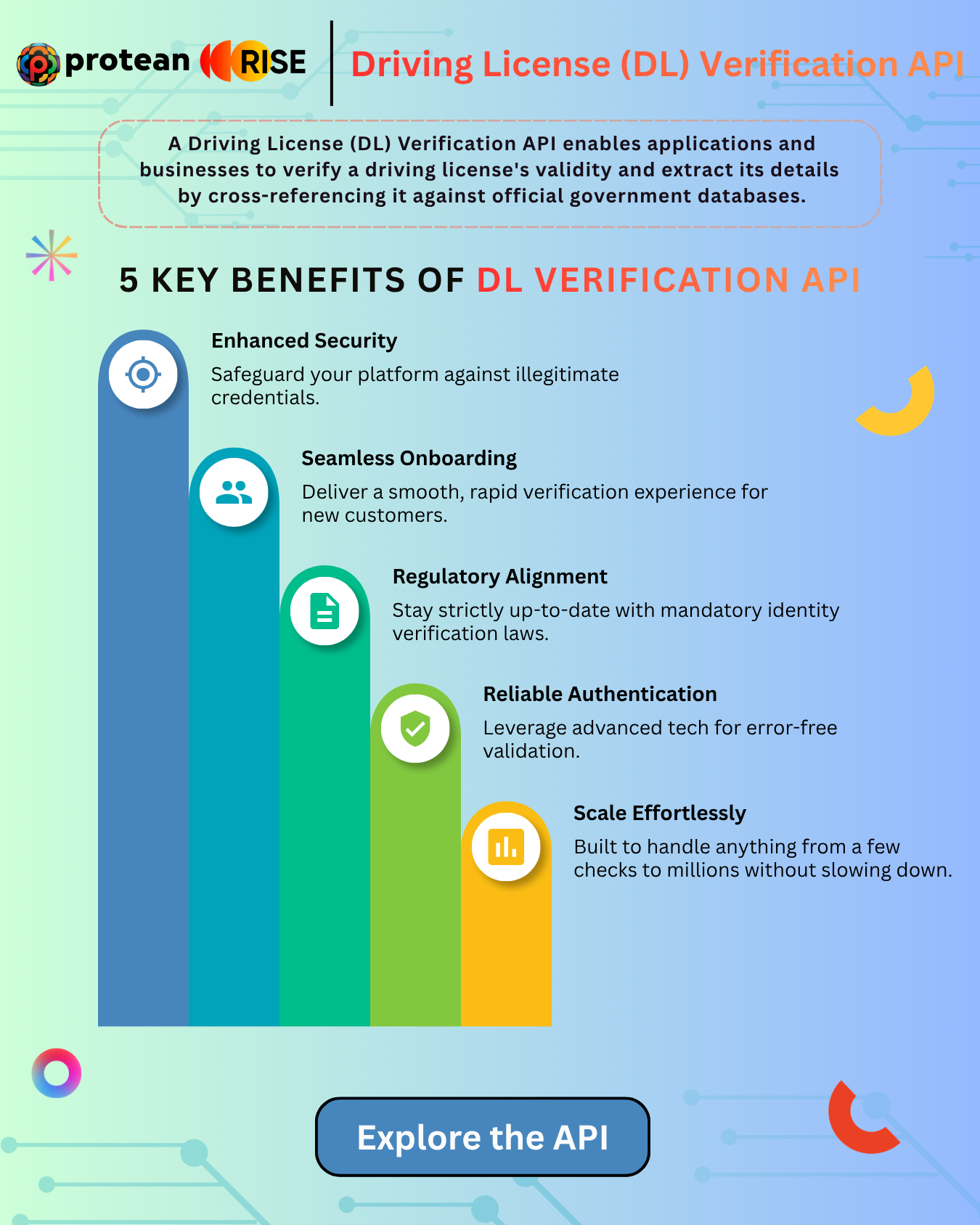
Benefits of Driving License (DL) Verification API
CSR Is Growing - Why Isn’t Impact Keeping Pace?
CSR in India has officially entered its Scale Era, with recent data showing that CSR spending by listed firms jumped by 23%, reaching ₹22,212 crore in FY25. This growth is driven by strong corporate profits and a commitment among top firms and public sector undertakings (PSUs) to give back to society.
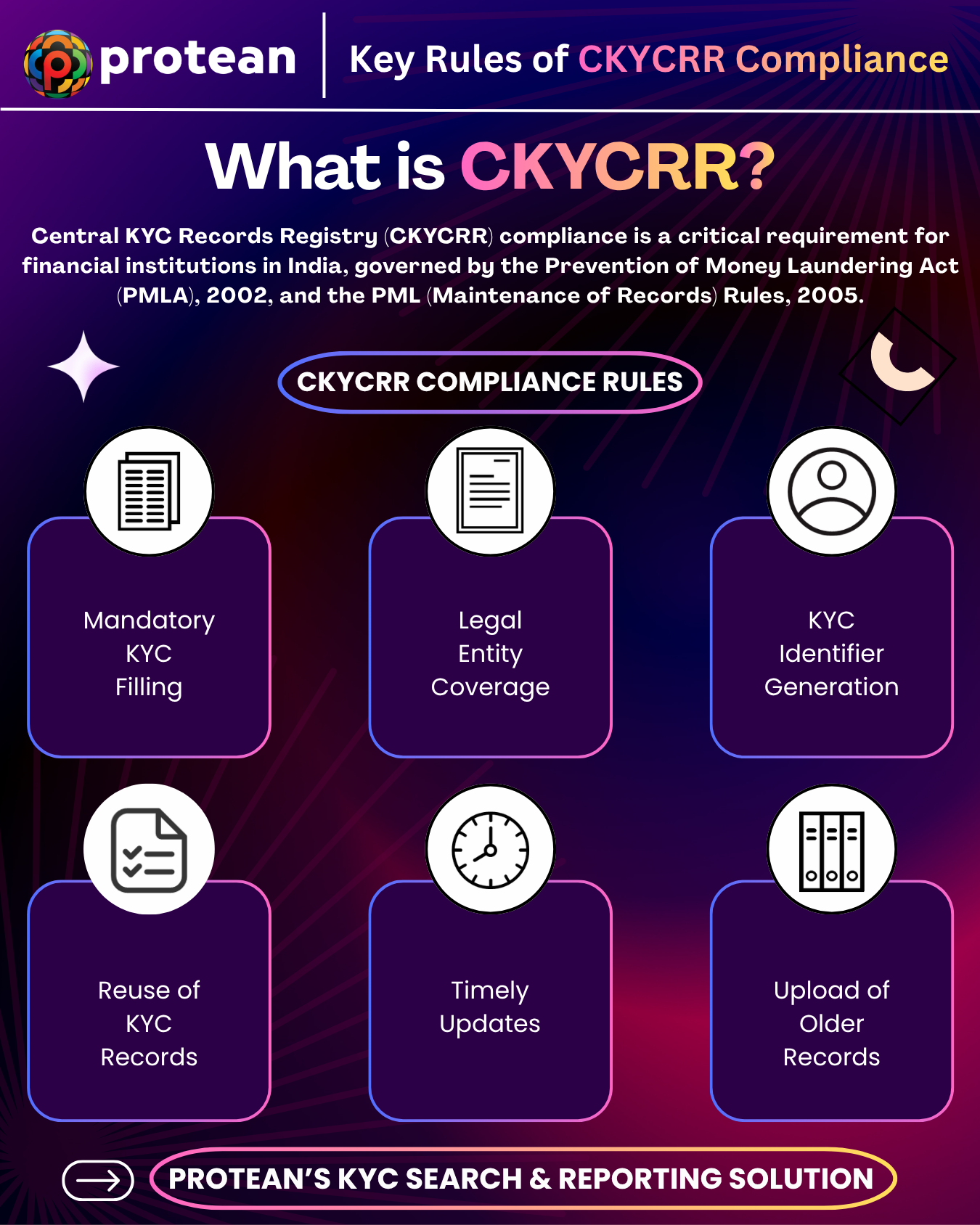
Key Rules of CKYCRR Compliance
The Importance of KYC on Social Media, Dating and Gaming Apps
Have you ever received a suspicious link from an anonymous profile? Or perhaps you've worried about who your teenager is interacting with in a multiplayer online game?
Today, there are growing concerns around fake identities, online fraud, and the misuse of anonymous accounts across digital platforms. In response to these escalating risks, a major shift is underway toward building safer and identity-backed digital ecosystems in India.
How to Download Udyam Certificate PDF Online in 2026
In India, businesses have transformed into a digital-first ecosystem where speed and trust are the primary focus. Your Udyam registration certificate is no longer just a piece of paper you file after registration, if you are an MSME owner. It has become an identity for your business.
Why Digital Onboarding Needs Driving License (DL) Verification API Providers
The risk is no longer just a "possibility"—it is a daily operational reality in 2026. Physical driving licenses have become easy to forge, manipulate, or misuse.
For businesses in logistics, mobility, or fintech, relying on manual document checks is risky. Manual verification exposes your organization to fraud, regulatory compliance risks, and operational delays.
Information Security Consulting
Unified Document Execution Layer: Why Enterprises are Moving Beyond Basic eSignatures
Finalizing a corporate contract involved printing pages, signing multiple sections manually, scanning the file, and emailing it back to the client just a decade ago. For a long duration, the basic eSignature was viewed as the terminal achievement of document digitization, solving the physical bottleneck of wet-ink signatures. It successfully reduced the reliance on physical mail, scanning, and physical documents.
Why MSME and Organization should focus on Corporate NPS
In today’s challenging market, a good salary is no longer sufficient to live a secured life. It demands more especially from the corporate employees. While large organizations have offered pension schemes long back, many Micro, Small, and Medium Enterprises (MSMEs) and mid-size organizations are yet to provide the similar benefits to their employees.