Background verification is one of the most important aspects for various businesses. High-stakes B2B industries depend on deep background verification. However, modern users demand quick, "one-click" experiences.
Lengthy background verification processes can lead to high abandonment rates and lost revenue for growing enterprises. Therefore, there is a need to shift from "Interruption-based verification" to "Integrated background checks."
With modern background verification APIs, security and speed can coexist. Now, financial institutions and tech platforms do not need to halt a transaction for identity validation. Here, the process occurs in the background while the user continues their journey.
The Architecture of an Invisible Onboarding Flow
The creation of an invisible onboarding flow begins with the collection of minimal Personally Identifiable Information (PII) upfront. Here is how the invisible onboarding flow architecture works.
- Shadow Processing - Without a user redirect, the system pings authoritative databases like UIDAI or the Income Tax department (ITD).
- API-First Design - With a modern API-first approach, businesses can validate credentials without the need for a third-party site visit.
- Real-Time Responses - The user does not hit a "Please wait 24 hours" wall, due to super quick response times.
A well-designed API integration can translate complex data checks into a simple "pass" or "fail" signal for the interface. Thus, the momentum of the onboarding journey can stay intact right from the first click to the final confirmation.
Implementing Risk-Based Verification
Smart systems can use risk scoring to determine the background verification depth required for each unique user. With risk-based verification, low-risk individuals can experience onboarding with limited manual intervention. Here is how the risk-based verification works.
- Automated Approvals - Users with a clear, established digital footprint can move through the "happy path" instantly.
- Standard Scrutiny - Average risk profiles go through basic identity and address checks against government records.
- Enhanced Due Diligence - High-risk profiles, such as those with inconsistent records would trigger a deeper investigation.
- Focus on Legitimate Red Flags - Automation can take care of a majority of verification approvals. Therefore, the compliance team can focus on legitimate red flags.
- Numeric Risk Score - The risk-based verification system assigns a numeric risk score. This score is based on data points such as GST history, MCA master data, and UAN records. This can considerably reduce a "one-size-fits-all" delay for every applicant.
- Granular Information - API suites provide the granular information required to build these sophisticated decision engines. With API systems, security can remain tight while the user experience remains effortless and personalised. The use of verified data sources can largely minimise the chances of identity fraud at the entry point.
Strategic API Integration for Depth
A strategic API integration can provide a comprehensive view of the user’s professional and financial standing. Here is more on how the strategic API integration can provide background verification depth.
- Real-Time OCR - Data is extracted from identity documents using Optical Character Recognition (OCR). This can instantly minimise manual entry errors.
- Continuous Monitoring - Background verification systems can perform ongoing checks rather than only a single point-in-time validation.
- Direct Data Flow - The background verification results can flow directly into the internal system of record, such as an HRMS or CRM.
Thanks to robust API integration, manual export and import of data seems to have become obsolete. This direct connection can reduce the risk of data leaks. It can also ensure that the information remains current.
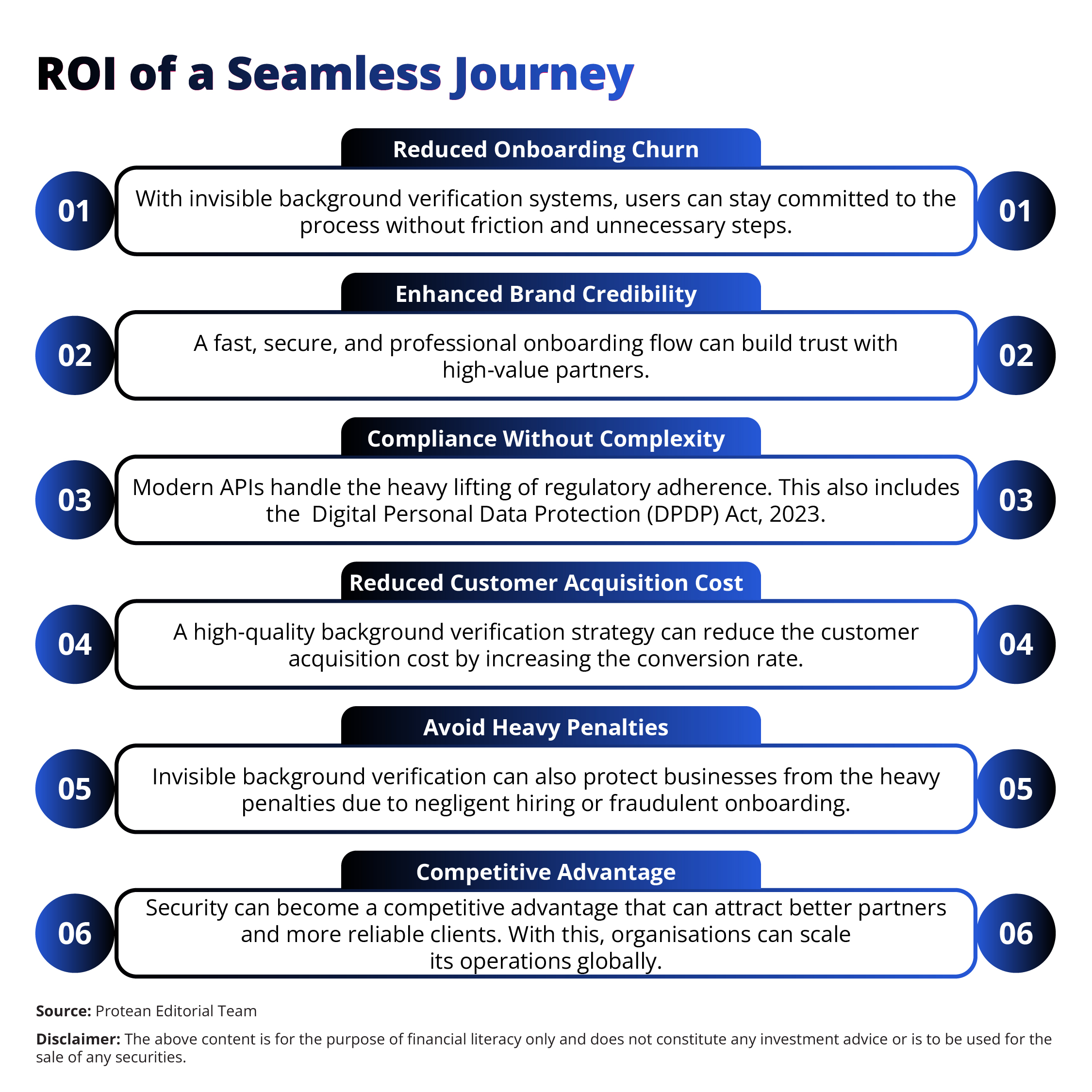
ROI of a Seamless Journey
The financial benefits of an invisible background verification process are important for any digital business. Here is how this background verification process can lead to seamless user journeys.
What is Important for Security & Data Privacy in 2026
Security protocols need to evolve to protect the sensitive data involved in background verification. Here are the important points for data privacy and security in 2026.
- Zero-Trust Architecture - In invisible or seamless background verification, every verification request follows strict authentication before it reaches the data source.
- End-to-End Encryption - As the data travels between business and government bodies, data remains encrypted at every stage.
- Consent Management - With digital consent journeys, users can maintain control over their personal information at all times.
Protean eGov Technologies emphasises the importance of secure API architecture to prevent unauthorised access. The RISE system creates an immutable, time-stamped audit trail for every consent given by the user.
Conclusion: The Future of Verification
In 2026, the industry is moving towards "Decentralised Identity." In this system, a background verification API can validate a pre-validated digital token.
This evolution can further simplify the journey for both the business and the user. A strong verification strategy is, thus, essential for any firm that values security and growth. Businesses can rely on a partner like Protean eGov Technologies can to stay ahead of fraud and regulatory shifts. They can transition to integrated checks for securing a sustainable future for the digital economy.
Frequently Asked Questions (FAQs)
Q1: Does a background verification check slow down the app experience?
No. Modern APIs can process requests in just a few seconds. So, the user can usually complete the next step of the form before the check finishes in the background.
Q2: Is background verification possible without asking the user to upload documents?
Yes. The system fetches details directly from government records through a secure API integration. The background verification system uses basic identifiers like a PAN or Voter ID number for the same.
Q3: How does risk-based verification improve the success rate of onboarding?
With risk-based verification, low-risk users might be able to go through quickly or skip the most intrusive checks. This can reduce the friction for the majority of applicants. Thus, it can lower the drop-off rate.
Q4: Can the system detect if a user provides a fake identity document?
A specialised background verification API makes use of liveness detection and face matching. Thus, the system can detect if the person is real and the document is genuine to a greater extent.