API programs usually fail in enterprises for a simple reason: trust is assumed in too many places. Teams verify at the perimeter, but not consistently across lifecycle stages such as design, deployment, runtime changes, and deprecation.
In cloud-heavy environments, that assumption becomes expensive. APIs connect customer journeys, partner platforms, internal services, and automated workflows. A weak trust model in one API can quickly become a business-wide problem in security, reliability, and compliance.
This is why zero-trust APIs are now an operating requirement. The objective is not to add one more security layer. The objective is to make API trust measurable, enforceable, and auditable across the full cloud lifecycle.
| Also read: Private Cloud Data Security |
Why This Is a Leadership Issue
Zero-trust APIs are often treated as a technical topic, but the impact is strategic. When API governance is fragmented, leadership loses three things first:
- Control clarity: teams cannot quickly prove which policies are active and where.
- Audit confidence: evidence is assembled reactively instead of generated continuously.
- Execution speed: partner onboarding and release cycles slow down because risk checks are inconsistent.
That is why governance, security, and compliance must be handled as one operating model around APIs, not three disconnected review tracks.
Where Zero-Trust API Programs Break Down
Most breakdowns are operational, not conceptual. Common failure points include:
- Inventory gaps: the organization cannot confidently list all active APIs, owners, and exposed data paths.
- Identity drift: service accounts, tokens, and machine identities accumulate permissions without regular lifecycle checks.
- Policy inconsistency: different environments enforce different trust controls for similar APIs.
- Runtime disconnect: API telemetry and incident workflows are not linked to lifecycle records and approval history.
- Ownership fragmentation: platform, security, and compliance teams each manage part of the flow, but no one owns end-to-end trust outcomes.
When these gaps combine, zero trust becomes a slogan rather than an operating capability.
What a Practical Zero-Trust API Model Looks Like
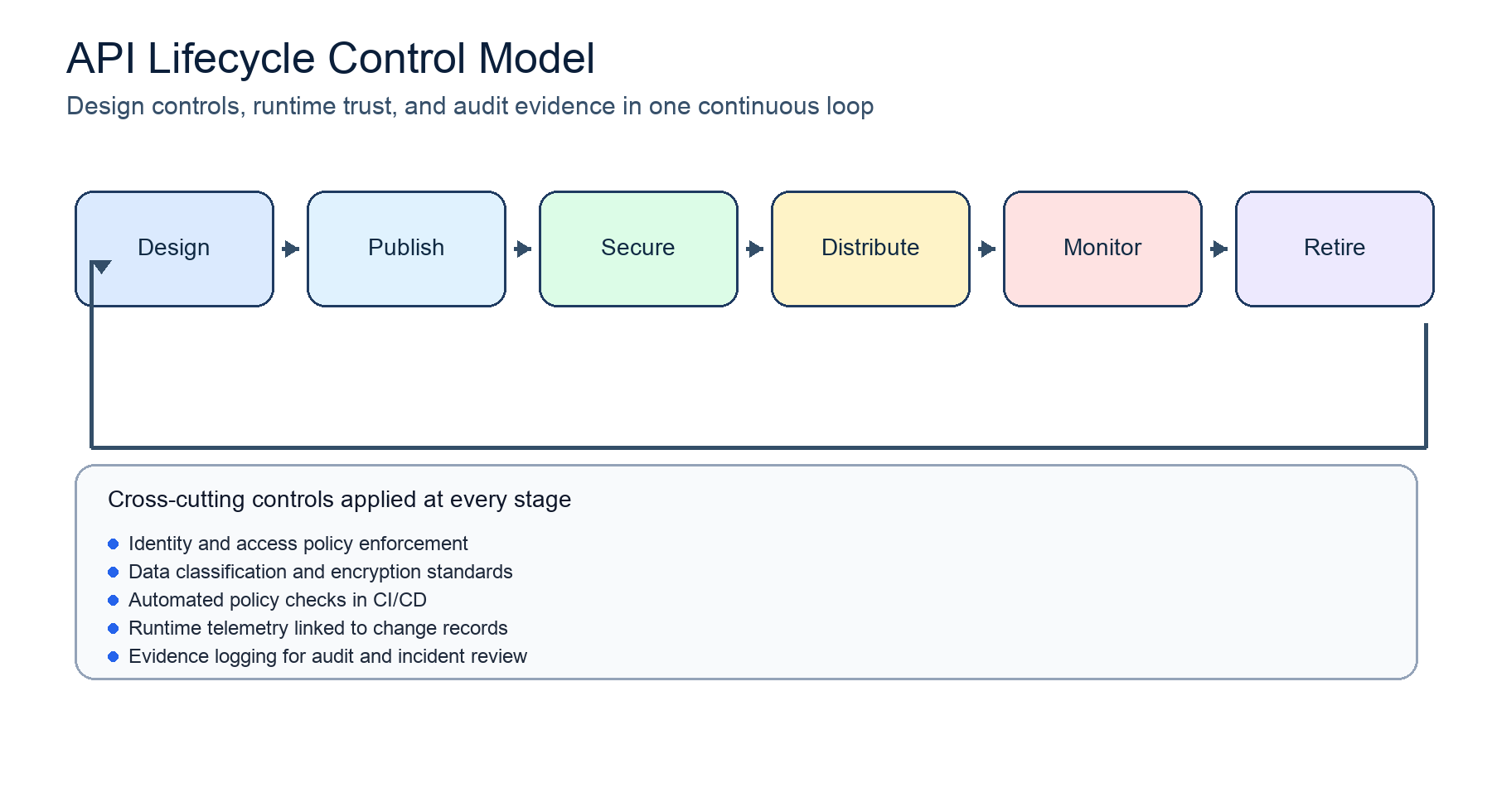
Figure 1. Lifecycle-led zero-trust controls for enterprise APIs.
A practical model keeps security strong without stalling delivery. It usually has five characteristics:
- Verified identity at every hop, including non-human workloads and service-to-service interactions.
- Policy-driven authorization tied to API context, sensitivity, and usage pattern.
- Lifecycle controls that apply from design to retirement, not only at runtime.
- Continuous observability linked to ownership, version history, and dependency maps.
- Evidence-ready records for audits, incidents, and control reviews.
This is where cloud infrastructure integration matters. Zero-trust API controls are more reliable when lifecycle, policy, and runtime telemetry run through one consistent operating path.
| Also read: API for Business Agility |
Integrating API Lifecycle Management With Cloud Infrastructure
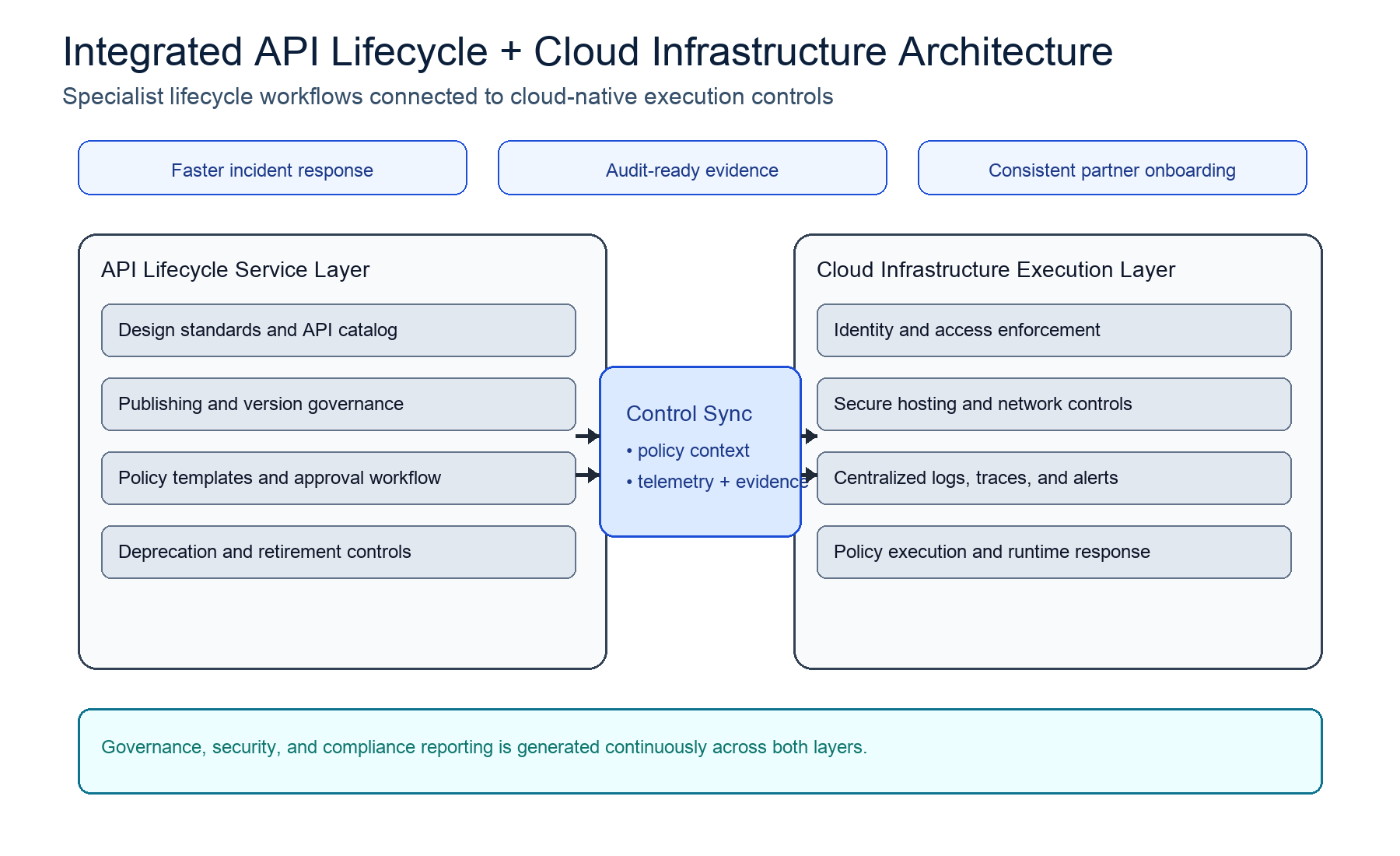
Figure 2. How lifecycle services and cloud execution controls stay in sync.
Enterprises often use specialist ecosystem partners for API lifecycle management because these programs require deep process maturity across design, security, publishing, change, and retirement.
The cloud layer must then provide the execution backbone:
- consistent hosting controls across environments,
- identity and access enforcement at scale,
- centralized logging and traceability,
- and reliable escalation paths for runtime events.
In this model, lifecycle service and cloud infrastructure are not separate decisions. They are two halves of one control system.
90-Day Execution Plan
A phased rollout helps teams improve trust controls without disrupting active delivery.
- Map APIs by business criticality, data sensitivity, owner, and dependency.
- Define mandatory trust gates for publish, change, and retirement workflows.
- Standardize machine-identity controls and permission review cadence.
- Connect runtime API telemetry with lifecycle records and exception tracking.
- Track a focused scorecard: undocumented APIs, policy exceptions, token sprawl, and time-to-evidence.
- Apply the same model to partner-facing APIs before onboarding scale increases.
This approach keeps zero trust practical: measurable controls, clear ownership, and steady delivery velocity.
Conclusion
Zero-trust APIs on cloud infrastructure are no longer a narrow security initiative. They are an enterprise execution model for reducing trust gaps while scaling digital services responsibly.
Organizations that treat API governance, security, and compliance as one lifecycle system achieve cleaner audits, faster incident triage, and stronger partner confidence.
For teams using partner-led API lifecycle services on environments such as Protean Cloud, the biggest advantage is consistency: trust controls remain enforceable across design, runtime operations, and growth.
FAQs
Q1: Is zero-trust API mostly a security control?
No. Security is central, but enterprise success depends equally on lifecycle governance, ownership discipline, and compliance evidence continuity.
Q2: Can zero trust work without slowing API delivery?
Yes, when controls are embedded in lifecycle workflows. Programs slow down only when checks are manual, late-stage, or inconsistent across environments.
Q3: What should enterprises fix first?
Start with inventory and ownership. If teams cannot identify which APIs exist, who owns them, and what policies apply, zero-trust enforcement will remain partial.
Q4: Why is cloud integration so important for API trust?
Because runtime trust decisions depend on infrastructure behaviors such as identity enforcement, logging, and policy execution. Without cloud integration, lifecycle controls lose reliability at scale.