India is rapidly moving towards fully adopting paperless transactions. Aadhaar eKYC solutions with UIDAI compliance are at the core of this transformation.
A robust Aadhaar eKYC provider is a strategic asset for any business aiming to scale in a hyper-competitive market. Currently, there’s a tightening of UIDAI compliance frameworks and the rise of sophisticated fraud vectors.
Chances of sophisticated frauds, face spoofing and identity fraud can be reduced with a considerably higher standard of verification. Generally, traditional methods can fail to meet the expectations of modern consumers who demand instant access to services.
Here’s a comprehensive roadmap for businesses to select an Aadhaar eKYC solution to balance legal strength with a seamless user experience.
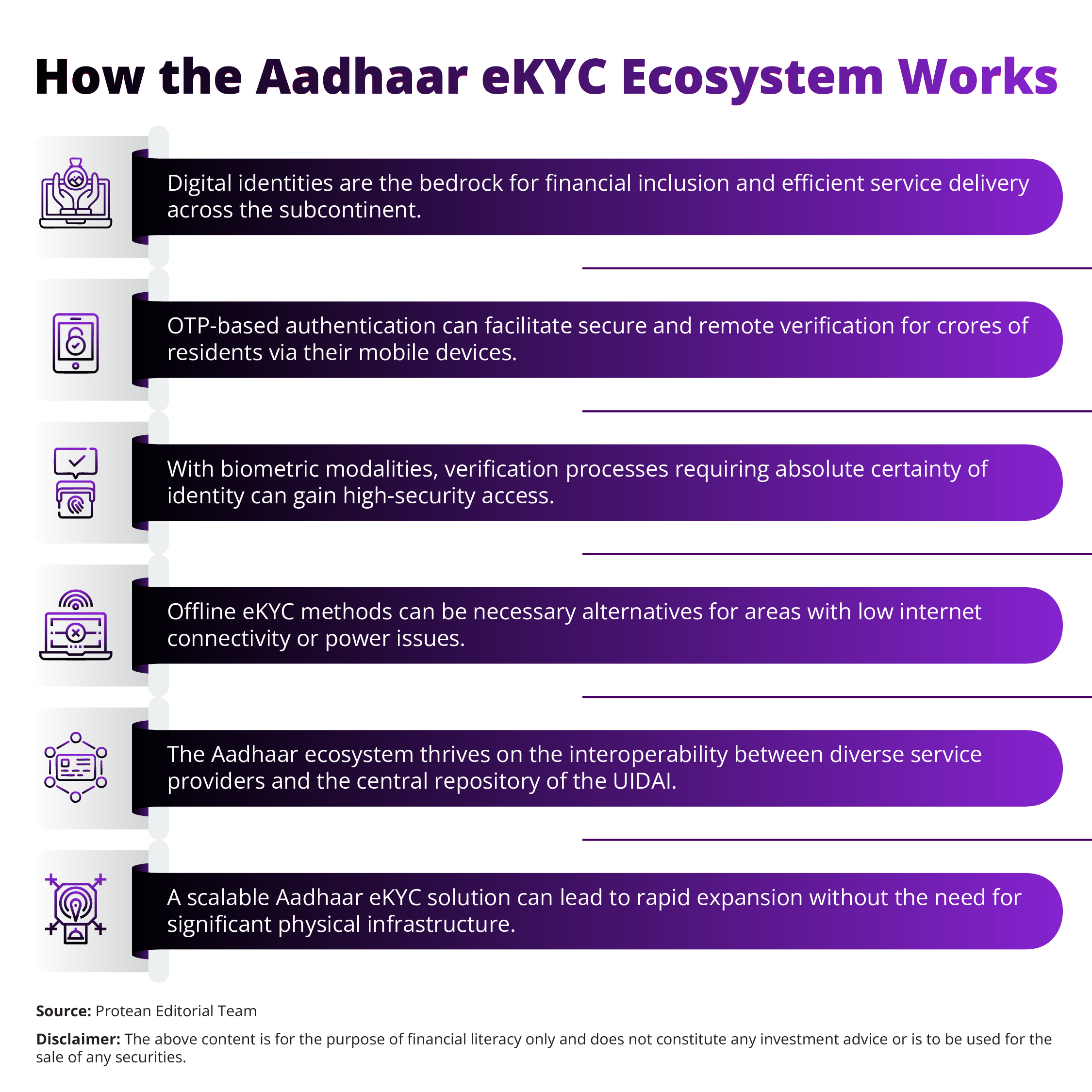
Understanding the Modern Aadhaar Authentication Ecosystem
Here is how the Aadhaar eKYC ecosystem works.
UIDAI Regulatory Mandates
Legal compliance is the most important factor for any entity utilising identity services. Here’s more on the evolving legal landscape.
- The Aadhaar Act of 2016 is the main legal framework for all Aadhaar-based verification activities in India.
- Service providers need to obtain explicit consent from the resident before they initiate every instance of verification.
- Data encryption is mandatory for all resident information both in transit and at rest.
- The Masked Aadhaar requirement can protect the privacy of the individual's full identity number on physical copies.
- With periodic audits organisations can maintain a high level of UIDAI compliance through regular inspections.
- Strict storage limitations prevent the unauthorised retention of biometric data or full identity numbers.
- Authentication logs record the purpose of every transaction for accountability and future dispute resolution.
- Sub-AUAs operate under the direct oversight of their parent agencies to maintain the highest standards.
- Circulars from the UIDAI provide real-time updates on technical and legal requirements to every registered entity.
- Heavy penalties apply to any violation of privacy or data security norms according to the law.
- Digital signatures on responses confirm the origin and integrity of the data received from the system.
- The Virtual ID is an option to use in place of the actual Aadhaar number for authentication.
Technical Performance and Scalability
Here’s how Aadhaar eKYC can offer robust technical performance and scalability.
Uptime and Reliability
Businesses use Aadhaar eKYC solutions with redundant server architectures. With minimal downtime, the onboarding process can stay active around the clock for users. Slow response times during peak hours can be managed with database replication, load balancing, and caching mechanisms.
Low Latency Responses
The modern customer journey in the digital age is led by speed.
- Efficient APIs can return verification results in milliseconds to minimise drop-off rates during the sign-up process.
- Secure and high-speed connectivity to the central servers is maintained through API gateways and TLS encryption.
Geographic Redundancy
Distributed data centers can protect the service against regional outages or natural disasters.
Robust infrastructure can maintain the flow of Aadhaar eKYC transactions across diverse geographies without interruption.
This resilience proves vital for national-level operations where consistency is crucial.
Advanced Features: Video KYC & Fraud Prevention
With the rise of remote onboarding, the adoption of more advanced security measures to maintain UIDAI compliance is important. Here are the advanced eKYC features to consider.
- AI-powered liveness detection can protect from spoofing attempts that use high-resolution photos or pre-recorded videos.
- Automated face-match technology can compare the facial image captured during authentication with the official image stored in the Aadhaar repository.
- The system would flag suspicious IP addresses to prevent organised fraud attacks from known high-risk zones.
- Machine learning is used by advanced Aadhaar eKYC solutions for identifying anomalous (unusual) behaviour during the user journey.
- The Aadhaar eKYC architecture can support a huge scale for the banking, insurance, and telecommunications sectors.
- It uses advanced encryption to protect sensitive resident data throughout the lifecycle of every transaction.
- Aadhaar eKYC solutions can also reduce operational overhead through high automation and low manual intervention rates.
Therefore, organisations relying on Aadhaar eKYC authentication can deliver a stable and secure verification experience for their customers.
All these advanced features can be integrated with Protean eGov Technologies’ comprehensive identity tools suite. Protean’s Aadhaar eKYC solutions can seamlessly integrate with existing enterprise systems for rapid deployment for various business units. Such eKYC platforms prioritise high levels of UIDAI compliance. They do this through continuous updates and rigorous security protocols meeting national standards.
Final Thoughts on Identity Strategy
It is important for businesses to select a high-quality Aadhaar eKYC provider as a strategic investment in the organisation's security, efficiency, and user experience. Sophisticated identity verification is the foundation of modern commerce and can protect both the entity and the consumer.
A business ignoring these could face significant legal and operational risks. Every decision-maker needs to evaluate their current infrastructure to stay ahead of regulatory shifts and technological advancements. Thus, by prioritising compliant infrastructure, high accuracy, and fraud prevention, organisations can ensure sustainable, high-growth digital scaling.
Audit the current verification workflow today to identify potential vulnerabilities in the system. Schedule a demo with a compliant Aadhaar eKYC solution provider to modernise your customer journey and secure your path to growth.